File:Firejail caps example.png
Original file (1,280 × 512 pixels, file size: 106 KB, MIME type: image/png)
Summary
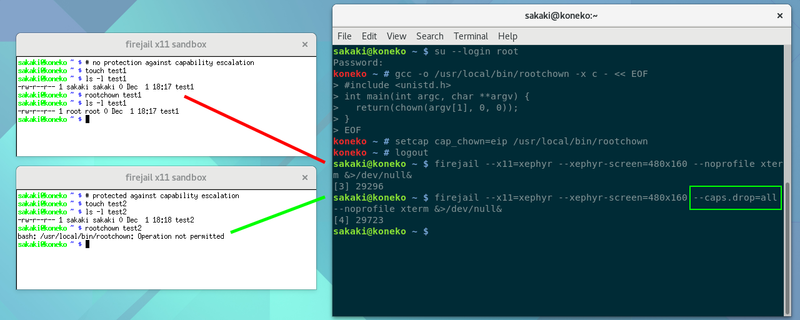
Screenshot of two xterms running in xephyr windows (started using firejail from the command line in parent desktop), in which running a cap_chown=eip program (rootchown) as a regular user is attempted, to illustrate firejail's ability to prevent privilege escalation. In the first xterm, the program is allowed to run, but in the second xterm (started with the --caps.drop=all firejail option) the program is aborted, with "Operation not permitted" error message. The program rootchown itself is trivial, and the source, compilation (as root) and necessary setcap command are shown in the screenshot also. Uploaded for use in a forthcoming mini-guide on X11 sandboxing (an addendum to Sakaki's EFI Install Guide).
Licensing
You are free to share (copy, distribute and transmit the work) and remix (adapt the work), but you must attribute the author and distribute any derivative works you create under a similar license.
File history
Click on a date/time to view the file as it appeared at that time.
| Date/Time | Thumbnail | Dimensions | User | Comment | |
|---|---|---|---|---|---|
| current | 18:49, 1 December 2017 | 1,280 × 512 (106 KB) | Sakaki (talk | contribs) | Screenshot of two xterms running in xephyr windows (started using firejail from the command line in parent desktop), in which running a cap_chown=eip program (rootchown) as a regular user is attempted, to illustrate firejail's ability to prevent privil... |
You cannot overwrite this file.
File usage
The following page uses this file:
